Android/Plankton.B!tr
 Analysis
Analysis
Android/Plankton.B!tr is a variant of Android/Plankton.A!tr which targets privacy on Android mobile phones.
Like Android/Plankton.A!tr, it consists in an intrusive form of advertisement capable of:
- replacing the browser's homepage
- adding application shortcuts
- adding bookmarks
- recording search queries for targeted advertisement
This particular version has the following differences with version A:
- It is located in the namespace com.apperhand (not com.plankton), with its protocol exposed in com.apperhand.common.dto.protocol.
- The samples display a user agreement (EULA) (see Figure below)
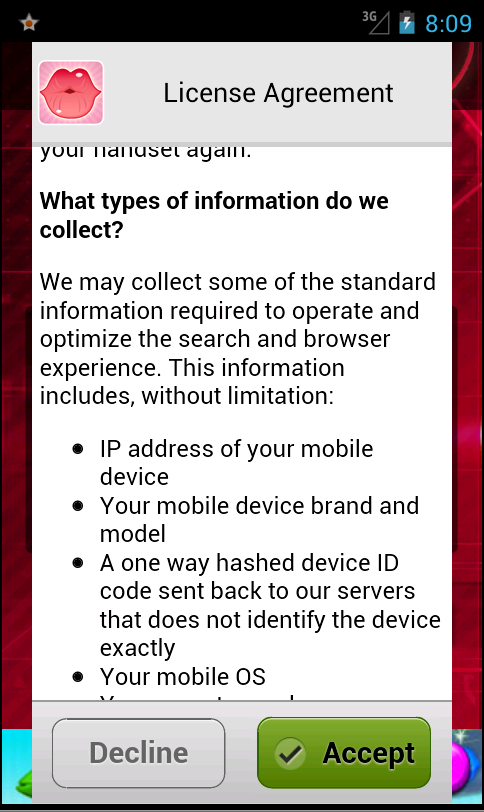
Figure 1. What information Android/Plankton.B!tr collects
When requesting an EULA, the sample posts an HTTP request to hxxp://www.apperhand.com with a JSON object containing:
- the Android ID
- device information such as brand, device, manufacturer
- OS information: version, display metrics, locale, user agent
- sample's package name
Once the end-user has accepted or declined the EULA, a request is sent to hxxp://www.apperhand.com/ProtocolGW/protocol/eulastatus. The POSTed information contains again multiple information including whether the end-user accepted the EULA or not:
"accepted":true
There is an ongoing debate as to whether those samples are Adware or Malware. The fact there is an EULA would indicate it is an adware. On the other hand, enforcing bookmarks/homepages/shortcuts is really abusive, and the protocol is quite extensible (including with risky features e.g Upgrade, DumpLog). Those elements rather match malware. For sure, anyway, end-users are probably better off without such applications, especially in terms of privacy.
 Recommended Action
Recommended Action
- FortiGate Systems
- Check the main screen using the web interface for your FortiGate unit to ensure that the latest AV/NIDS database has been downloaded and installed on your system - if required, enable the "Allow Push Update" option.
FortiClient Systems
- Quarantine/delete files that are detected and replace infected files with clean backup copies.
 Telemetry
Telemetry
Detection Availability
| FortiGate | |
|---|---|
| Extreme | |
| FortiClient | |
| Extended | |
| FortiMail | |
| Extended | |
| FortiSandbox | |
| Extended | |
| FortiWeb | |
| Extended | |
| Web Application Firewall | |
| Extended | |
| FortiIsolator | |
| Extended | |
| FortiDeceptor | |
| Extended | |
| FortiEDR |